Law enforcement agencies in the United States, Germany and Canada coordinated on a comprehensive disruption operation designed to seize infrastructure used by four large botnets.
The Justice Department announced on Thursday evening that the Aisuru, KimWolf, JackSkid and Mossad botnets were used to target victims with destructive distributed denial-of-service attacks. This action aimed to stop malicious actors from overwhelming websites and making them unreachable for legitimate users globally while protecting critical infrastructure from further compromise. The operation represents a significant victory in the ongoing effort to dismantle organized cybercriminal networks that rely on compromised hardware.
The four botnets were composed of approximately three million compromised devices around the world, many of which are Internet of Things devices like cameras and routers. Court documents stated there were hundreds of thousands of devices compromised in the United States alone during the campaign against online infrastructure. These networks sold access to cybercriminals, who used them to launch coordinated attacks or mask other criminal activity online for profit. The scale of infection demonstrates the vulnerability of unsecured consumer hardware to remote exploitation by malicious actors.
The KimWolf and JackSkid botnets were known to also target devices that were behind standard firewalls effectively using residential proxy techniques. Operators utilized novel techniques to infiltrate home networks through compromised devices including streaming TV boxes and video recorders. This technique allowed the operators to compromise millions of devices globally, growing to over two million infected devices according to Amazon executives who analyzed the threat. Such methods bypass traditional perimeter defenses by using trusted residential IP addresses.
Prosecutors reported that the Aisuru botnet issued more than 200,000 DDoS attack commands during its active operation window against various targets. The KimWolf botnet issued more than 25,000 commands while the JackSkid botnet launched more than 90,000 commands against various targets. The Mossad botnet launched more than 1,000 attack commands, collectively causing significant disruption to online services and networks worldwide. These figures illustrate the sheer volume of malicious traffic generated by the automated infrastructure.
Victims of the DDoS attacks lost hundreds of thousands of dollars through remediation expenses or ransom demands from hackers demanding payment. The Justice Department said multiple U.S. registered internet domains and virtual servers were seized through warrants executed by the Department of Defense. The Department of Defense Information Network had IP addresses that were targeted by DDoS attacks launched through the botnets during the campaign. Financial losses included both direct costs for system recovery and indirect costs from service downtime for businesses.
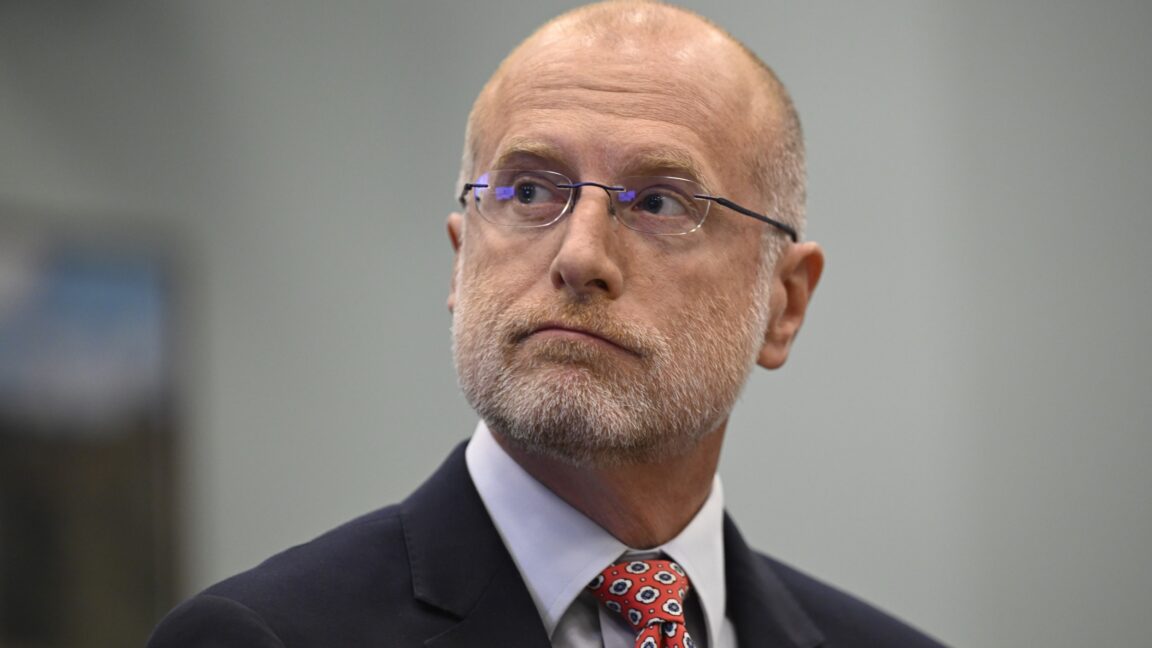
Amazon vice president Tom Scholl said the company helped identify the botnet command-and-control infrastructure and reverse engineered the malware. Scholl noted that KimWolf was a novel botnet because it targeted residential proxy networks specifically to bypass traditional defenses. He stated this technique allowed operators to compromise local networks typically protected from external threats by home routers and firewalls. Tech companies play an increasingly vital role in identifying and neutralizing these sophisticated threats.
Companies like Cloudflare have warned for years about Aisuru and Kimwolf, writing in recent months that the botnets had more than one million devices. They noted these networks could launch attacks that could cripple critical infrastructure or crash most legacy cloud-based DDoS protection solutions. This highlights the evolving sophistication of botnet operators targeting residential internet connections for power and scale. The industry continues to monitor these evolving threats closely to prevent future large-scale disruptions.
Law enforcement agencies continue to target botnets with infrastructure seizure operations and arrests due to how frequently they are used by cybercriminals. Botnets like QakBot, IPStorm and DanaBot have faced law enforcement scrutiny since 2021 as part of a broader crackdown on malicious infrastructure. Last week, the US partnered with Europol to take down a cybercriminal platform that offered access to the AVRecon botnet. These coordinated efforts signal a sustained commitment to protecting the digital ecosystem from organized crime and state-sponsored actors.
The Justice Department did not say if any arrests were made in conjunction with the infrastructure takedown at this time. Cybersecurity journalist Brian Krebs identified at least one alleged operator behind the botnets living in Canada earlier this year. This operation underscores the necessity of international cooperation in combating complex digital threats effectively across borders. Future investigations may reveal additional participants involved in the command-and-control structure of these networks.