The U.S. Cybersecurity and Infrastructure Security Agency issued a formal warning Thursday following a significant cyberattack on medical technology firm Stryker. Federal officials confirmed that malicious actors utilized compromised credentials to access Microsoft Intune management systems for the first time in this context. This unauthorized access resulted in the mass deletion of data across thousands of employee endpoints globally, disrupting internal communications immediately.
Hackers gained entry through the Windows-based network infrastructure and abused their privileges to trigger remote wipe commands across the fleet. Stryker confirmed on March 11 that the incident caused global disruption to its internal operations and external shipping systems. The breach did not involve malware or ransomware, distinguishing it from typical extortion campaigns seen in recent years.
Network administrators must ensure that specific user accounts with access to endpoint management tools require dual approval for high-impact actions. CISA advised that wiping devices or making sensitive configuration changes should trigger a second administrator verification step. This protocol aims to prevent a single compromised credential from destroying an entire organizational fleet of hardware.
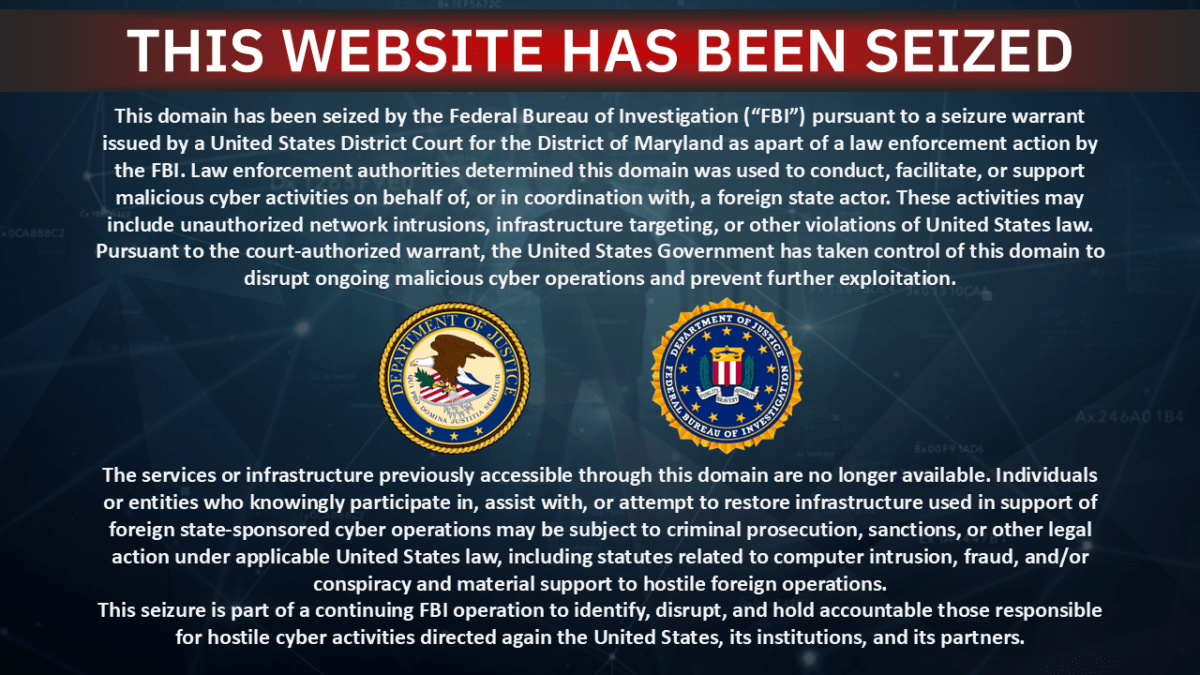
The group known as Handala took responsibility for the attack, claiming retaliation for a United States airstrike that killed dozens of children in Iran. This pro-Iran hacktivist faction alleged they extracted large volumes of data from the company network. The FBI subsequently seized the group's website on Wednesday according to reports from TechCrunch.
Medical device functionality remains operational despite the significant downtime affecting administrative and supply chain infrastructure. Stryker stated that recovery efforts are underway but has not provided a specific timeline for full system restoration. Employees connected to the network face ongoing challenges accessing personal and work-related devices remotely.
This incident highlights the critical risk associated with centralized device management platforms in large enterprise environments. Security teams must scrutinize privilege escalation vectors within identity and access management systems immediately. Previous breaches have shown that cloud-based endpoints often serve as the primary attack surface for advanced persistent threats.
Industry analysts suggest that the vulnerability lies in the lack of strict separation of duties for IT administrators managing fleet devices. Without proper governance, a single insider threat or stolen credential can cascade into widespread operational paralysis. Companies utilizing similar Microsoft solutions should prioritize immediate auditing of administrative access logs.
The breach underscores the necessity for robust identity verification and real-time monitoring of administrative actions across all cloud services. Organizations should consider implementing strict conditional access policies to limit the reach of compromised accounts. Failure to enforce these controls could result in similar catastrophic losses for other sectors dependent on supply chain logistics.
Legal and regulatory bodies may soon scrutinize the incident regarding data protection compliance and incident response timelines. Stakeholders will watch closely for any announcements regarding the security posture of other healthcare technology providers. The situation remains fluid as investigators work to determine the full extent of the data exfiltration claims.